Security, Governance & Compliances
- Manage cloud risks
- Protect cloud assets
- Accelerate growth
More numerous and advanced threats, more nebulous and complex compliance requirements, more difficult and intricate infrastructure to secure. Simply put: keeping data, workloads, and users secure is more than a full time job and organizations are having trouble keeping up. For even the most adept IT and Incident Response teams, effectively handling patching, malware threats, and intrusion detection can be too difficult to manage without expert help.
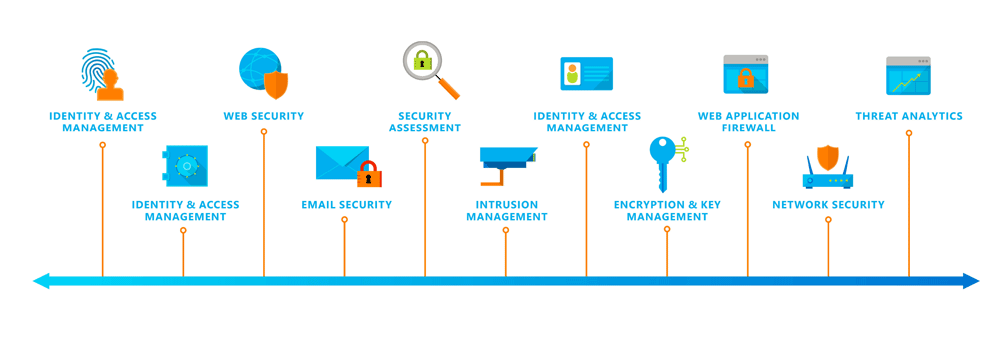
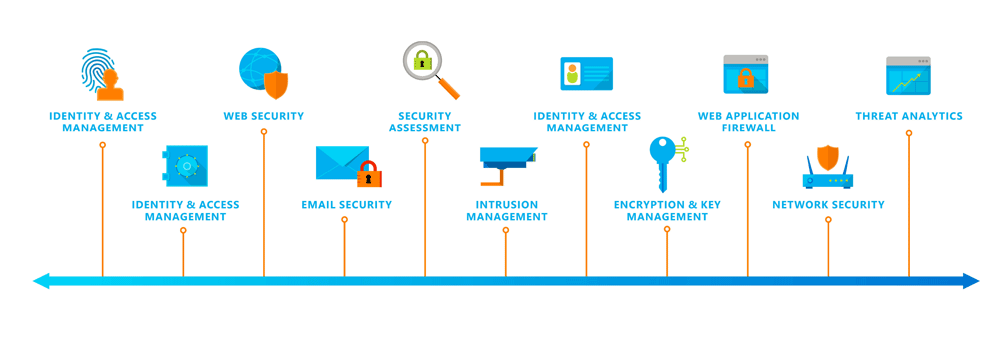
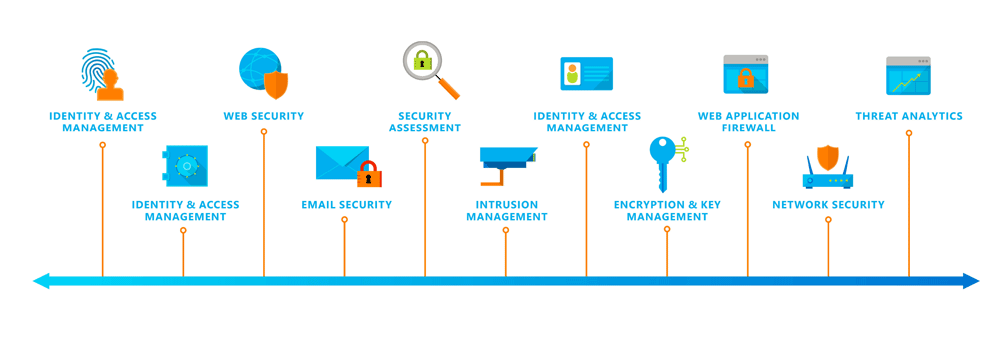
Crozaint has leveraged its decades-long experience to create a robust set of security technologies and practices. We ensure that your cloud infrastructure is resilient to attack, safeguards user access to the cloud environment, and helps keep customer data secure through encrypted communications as well as threat management and mitigation practices, including regular penetration testing.
Eliminate passwords, use multi-factor authentication, move to risk-based conditional access
Proactive notification of suspicious behaviour and unusual authentications
Automatically elevate access requirements based on risks
Device encryption, management of devices, consistent compliance
Auto-identify suspicious or compromised endpoints
Block, quarantine suspicious devices
Identify unsanctioned apps and enforce policies on cloud resources, monitor cloud data
Detect any deviations from baseline, policies, or behavior
Deploy new controls and block risky apps
Policy-based data separation, containment, classification, and encryption Proactive
Notification of any attempts for unauthorized data access
Revoke unauthorized access to documents, wipe device data
There is no easy answer to this and customers expect their service providers to solve it for them. Most mid-market and enterprise organizations simply do not have the time, resources, or dedicated staff required to monitor every aspect of IT, and this is where crozaint can add value as Cloud MSP.
Monitor Cloud and On-Premises Infrastructure from a Single Platform
Monitor, Trend and Alert on Cloud Resource Consumption
Monitor the End User Experience
Integrate Metrics, Flows and Logs for a Complete View
Complete monitoring of VMs, CPU utilization, memory usage, storage IOPs, and OS performance. Includes monitoring of application performance and operation health, and dashboards and reports on system health.
A view into your database that helps ensure high availability of database servers. The process involves keeping logs of size, connection time and users of databases, analyzing use trends, and leveraging data to proactively remediate issues.
Every client, device, and user accessing a network produces data that is logged. Analyzing those logs can offer deep insight into performance, security, resource consumption, and a number of other meaningful metrics. Powerful log management tools collect, correlate, and visualize all the machine data from multiple systems in one place.
End-to-end tracking of all aspects of an application (or webpage). App monitoring involves watching every part —from shopping carts to registration pages— of your app(s) for performance issues in an effort to provide the best user experience possible.